Wubes: Leveraging the Windows 10 Sandbox for Arbitrary Processes
tl;dr
Wubes is like Qubes but for Microsoft Windows. The idea is to leverage the Windows Sandbox technology to spawn applications in isolation. We currently support spawning a Windows Sandbox for the Firefox browser with other applications easily added.
Rational
The rational is if you browse a malicious site, it won't be able to infect your Windows host without additional chained exploits.
This means attackers need 1, 2, 3 and 4 below instead of just 1 and 2 in the case of Firefox:
- Browser remote code execution (RCE) exploit
- Local privilege exploit (LPE)
- Bypass of Code Integrity (CI)
- HyperV (HV) elevation of privilege (EoP).
Prerequisites
You need to have Windows 10 Pro or Enterprise and follow the quick start from here.
Usage
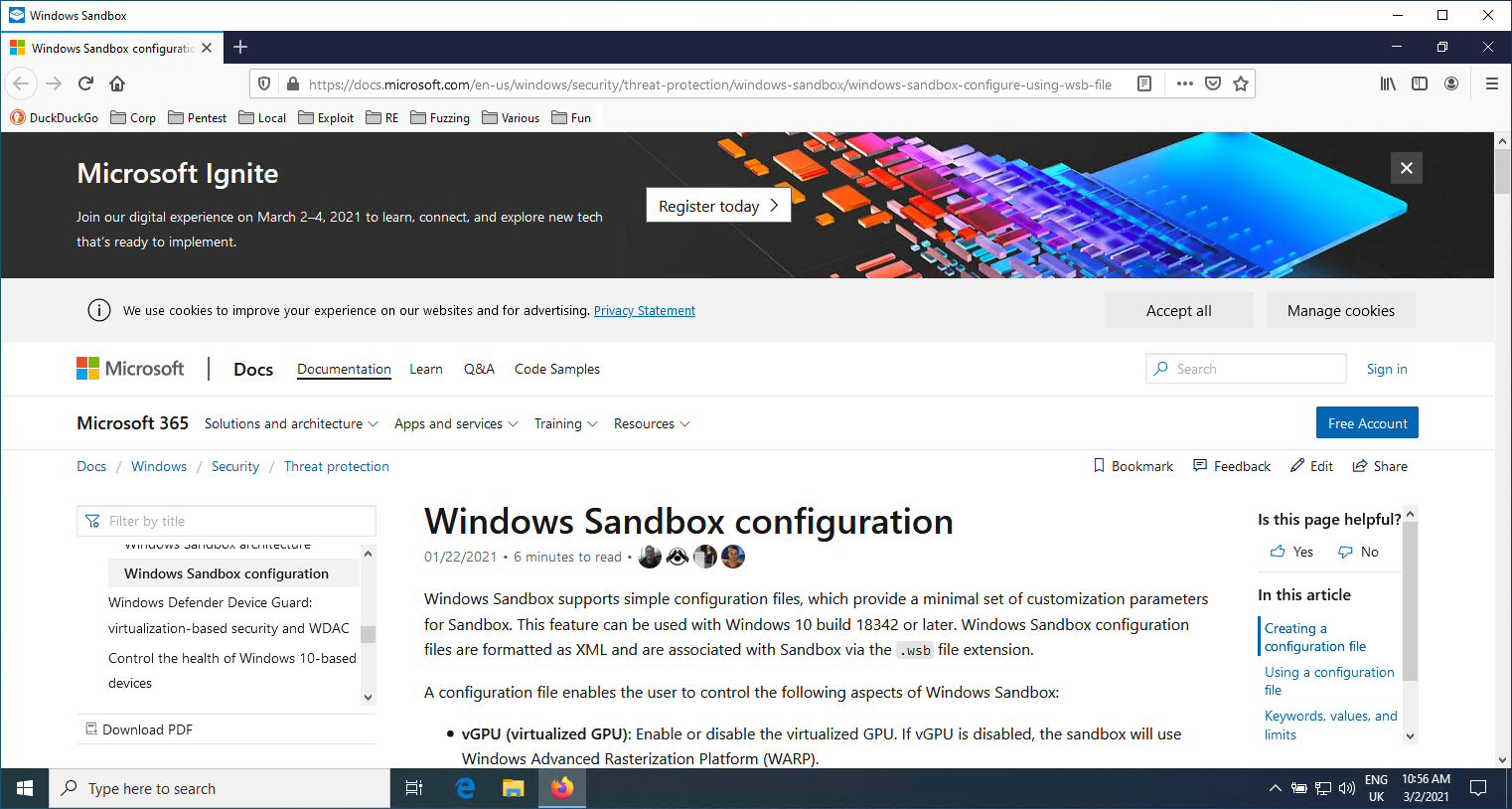
Each application has a Windows Sandbox profile (e.g. Firefox.wsb) that defines the host folder where wubes files are (you need to modify it to match your environment), as well as paths inside the Sandbox that will always be the same (no need to modify them).
<Configuration>
<vGPU>Enable</vGPU>
<Networking>Default</Networking>
<MappedFolders>
<MappedFolder>
<HostFolder>C:pathtowubessandboxesFirefox</HostFolder>
<ReadOnly>false</ReadOnly>
</MappedFolder>
</MappedFolders>
<LogonCommand>
<Command>C:usersWDAGUtilityAccountDesktopFirefoxinstall.bat</Command>
</LogonCommand>
</Configuration>
When we open the Windows Sandbox Profile (e.g. Firefox.wsb), it will automatically call the install.bat script to download Firefox, run Firefox once to create an empty profile, then replace the profile with the one from the shared folder and re-run Firefox. For this to work, you first need to copy the Firefox profile you used on your host (e.g. %APPDATA%MozillaFirefoxProfilesd63zctv5.default-release) into wubessandboxesFirefoxabcdefgh.default-release. We use hardcoded abcdefgh so you don't have to modify internal helper scripts.
You can see the Bookmark toolbar contains all my bookmarks and it re-opened an old tab.
Once we are done browsing the Internet, we can execute the C:UsersWDAGUtilityAccountDesktopFirefoxsave.bat file from inside the sandbox. That will backup our Firefox profile onto the host. We can then close the Windows Sandbox window.
Getting it
You can get the configuration here - https://github.com/nccgroup/Wubes